Being as pirate radio is, well, illegal, operators like to stay anonymous. At least ops who want to avoid the FCC. Naturally, most ops consider keeping their location secret very important. Some even go so far as subtly, or not so subtly, providing false clues about their location, in an effort to fool the radio authorities. Unfortunately, basic rules of radio propagation make this futile.
A warning in advance. I’m going to be discussing some basic shortwave radio propagation theory. Nothing here is brand new, or unknown to anyone in the radio field. Certainly not the radio authorities. Some fur… err… feathers are possibly going to be ruffled by what is presented below, possibly with loud protests of “destroying pirate radio” and “releasing the identities of operators”. Nothing could be further from the truth. This is Propagation 101 stuff. If it scares you, then you probably shouldn’t be operating a pirate radio station. The purpose is the educate listeners and operators, so they know exactly what information can be gleaned from observing signal reports. It’s better to know exactly what can be done with this information, than to stick your head in the sand and pretend it doesn’t exist.
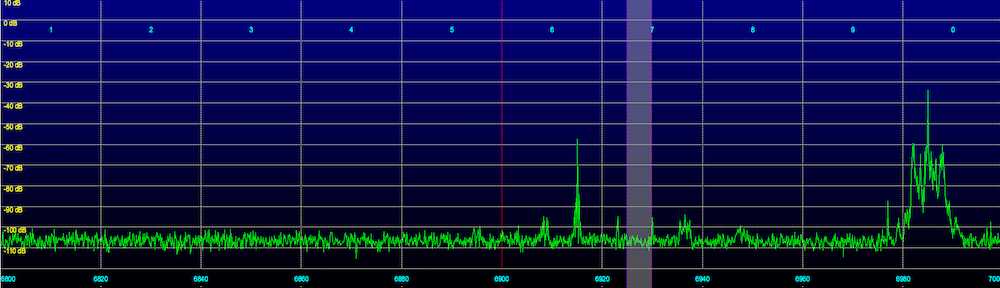
As has been discussed on this blog many times before, daytime propagation on the 43 meter band (where 6925 kHz is located) is considered NVIS (Near Vertical Incident Sky Wave). The radio waves go up, and are reflected back to the Earth for a fairly short distance around the transmitter site, usually a few hundred miles at the most. Attenuation by the D layer limits distant reception. At night, it’s almost the opposite reception pattern, as the D layer fades away, allowing distant reception. And the weaker F layer limits or eliminates NVIS reception, resulting in a skip zone around the transmitter, where the signal cannot be heard. The resulting reception area is shaped roughly like a doughnut.
So, for a daytime transmission, if one looks at a set of reception reports (as well as “no reception” reports, which can be equally useful), it becomes very easy to guesstimate about where a transmitter is. Not exactly of course, or even to a particular state, but certainly within a hundred miles or two. There will be a cluster of strong reception reports around the transmitter site, out to a few hundred miles. The maximum reception distance will vary a lot with transmitter level, antennas, and propagation conditions, but is likely under 1,000 miles. Look at where all the reports are coming from, especially the strong ones, find the center, and you have a good guess as to where the transmitter is.
At nighttime, listeners too close to the transmitter site (in the skip zone) will hear nothing, or at best a very weak signal. And during the transition from NVIS to DX propagation (see Going Long and An Interesting Example of a Station Going Long) the received signal will start to peak, and then suddenly cut out. Observing when this happens at a variety of listener sites provides other clues as to the transmitter location. If the F layer height and ionization values are known (and they are available in real time online) the distant to the station can be roughly determined when the station goes long. Do this for several receiver locations, and you can guess about where the transmitter is.
One ruse some operators have used in the past is to give misleading reception reports with a low signal level, using their real name and location, as just a regular listener. This is extremely dangerous, as if anyone is paying attention, their very weak signal report can stand out like a sore thumb if there are reports from others in the same area, with much stronger signal levels. Likewise, if you’re an operator, providing a completely bogus QTH doesn’t fool the FCC one bit. Announcing a QTH out on the Great Plains, while you’re really on the East Coast, doesn’t fool anyone when you’re being heard on the East Coast with an S9 signal at local noon. It just reminds everyone that you failed PROPAGATION 101. While shortwave propagation can be odd at times, there are limits. The laws of physics still must be obeyed.
The FCC and other radio enforcement agencies of course don’t have to rely on crude techniques such as these to locate transmitters. They have modern DFing equipment that can quickly and accurately locate a pirate station. The only reason they haven’t busted a given pirate is because, (as much as this may hurt to hear) that pirate is not important enough to get a visit. For now.
The commercially available WJ-9012 HF Direction Finding System, for example, boasts an error of less than 2 degrees. At a distance of 200 miles, that’s about 7 miles. Presumably the FCC has much better equipment.
While not announcing your location is probably a good idea (if for no other reason than to come across as taunting the FCC), in reality it doesn’t do too much to protect you from the radio authorities. Not interfering with allocated radio services, especially government and military, as well as operating from random remote locations, will go a long way to avoid getting The Knock.
Keep Safe!
The FCC has been DFing HF signals since WWII and should have little problem locating the transmitter site to some degree of accuracy. FCC operates remote receivers around the country, remotely controlled now from the Columbia Operations Center adjacent to the labs:
http://www.flickr.com/photos/fccdotgov/4797118284/in/set-72157624502681054
Physically visiting the transmitter site is another matter. That takes humans to get in fueled vehicles and travel. It costs money that may be spent if it is an FM pirate but less likely if it is an HF station.